There’s going to be a time when you’ll need to dig a little deeper into the flow of communication traversed through the Netscaler. I found the following commands and tools very helpful which I’m going to walkthrough a wee bit.
1# Show connectiontable,
Similar to getting directions from your Grandmother.
If you want to ensure that clients are establishing connection to your Virtual IP’s in quick and easy way, you can view the connection table on the Netscaler example below.
Figure 1.

Note: if you don’t want to use a expression filter you can simply use grep –i “” like the following
Command: show connectiontable | grep -i “10.7.?.113” |grep -i “HTTP”
2# nstcpdump,
Similar to Google maps it’ll get you there, but you might miss that off ramp.
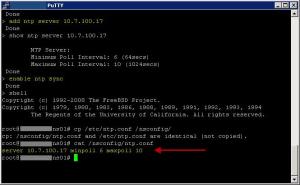
A good way to view the network activity of a particular host you can use nstcpdump.sh which can be very helpful for low level troubleshooting.
– The benefit using this command is that it has the ability to send packet capture data directly live to standard output.
Note: The following Citrix KB will equip you with all you need to know
http://support.citrix.com/article/CTX118185
We found ourselves using nstcpdump when we needed to verify if any arp packets where being submitted via a particular gateway / route.
Figure 2. Remember to you’ll need to shell in 1st, -X option displays the content of each packet.


3# nstrace,
Pinpoint navigation the Tom, Tom of the Netscaler packet analysis world
At times, you might need the complete output of the nstrace.sh script for a full analysis of a particular issue.
– It allows capturing packets in the native trace format, which provides NIC device information including device number and whether the packet was transmitted or received.
– It provides connection link information, allowing for the identification of links between client to vserver and SNIP/MIP to server tcp connections.
Note: The following Citrix KB will equip you with all you need to know
http://support.citrix.com/article/CTX122294
And if ever in the situation where you’ll need to manually stop a trace process quick read the following
http://support.citrix.com/article/CTX128889
Figure 3. To stop a trace press Ctrl + C will kill the process within your putty session.

If your requirement is to see communication from all Netscaler owned IP addresses it’s properly better to execute the trace without any filters and within your packet analyzer perform the necessary filtering. You’ll need to download the trace file by using the GUI simply enough see the following.
Figure 5.

Note: Once you have downloaded that trace file, its packet analyzing time goto http://www.wireshark.org/
There are great video’s to get you started in understanding the utility some screens I have provided demonstrating this great tool.
Figure 6. Press Ctrl + F The following will assist you finding the source IP of your client requesting a particular service.

Figure 7. The following screen shot demonstrates the flow of communication from the client request to the backend servers. For easy of viewing you’ll be able to apply filters and even follow the TCP Stream.

I hope this has proven helpful.